WORK FROM HOME SOLUTIONS
The world is facing a global lock down due to the COVID-19 outbreak. In response to this evolving pandemic, most organizations have initiated (or are being encouraged to implement) work from home plans for their employees to keep the business running, while practicing social distancing to limit the spread of the virus.
At IT Monteur, we understand that working from home may be a sudden transition for your organization, as well as your employees. Your business processes will need to be updated to support your work from home plans. And the work environment of your employees need to be optimized and secured as well. Moreover, you will need solutions that improve your team’s productivity while driving the overall profitability of your business.
To this effect, IT Monteur introduces the Work from Home Solutions to support your organization’s work from home needs. Our solutions are designed to optimise your team’s productivity while working securely from home.
How can IT Monteur Help you?
You need a trusted partner who can help you navigate and choose the right solution from the plethora of options available right now. IT Monteur can do that for you.
With our experience and expertise in providing solutions and services, we can help you adopt a powerful and secure Work from Home solution for your employees, based on the specific needs of your organization.
Our goal is to manage time efficiently in this adoption process, and focus on boosting your team’s productivity while working from home. We start by understanding the objectives, and studying your IT landscape and security policies. Based on that, we recommend solutions and services that will fulfil our goals.
Take a look at our solutions and services listed below.
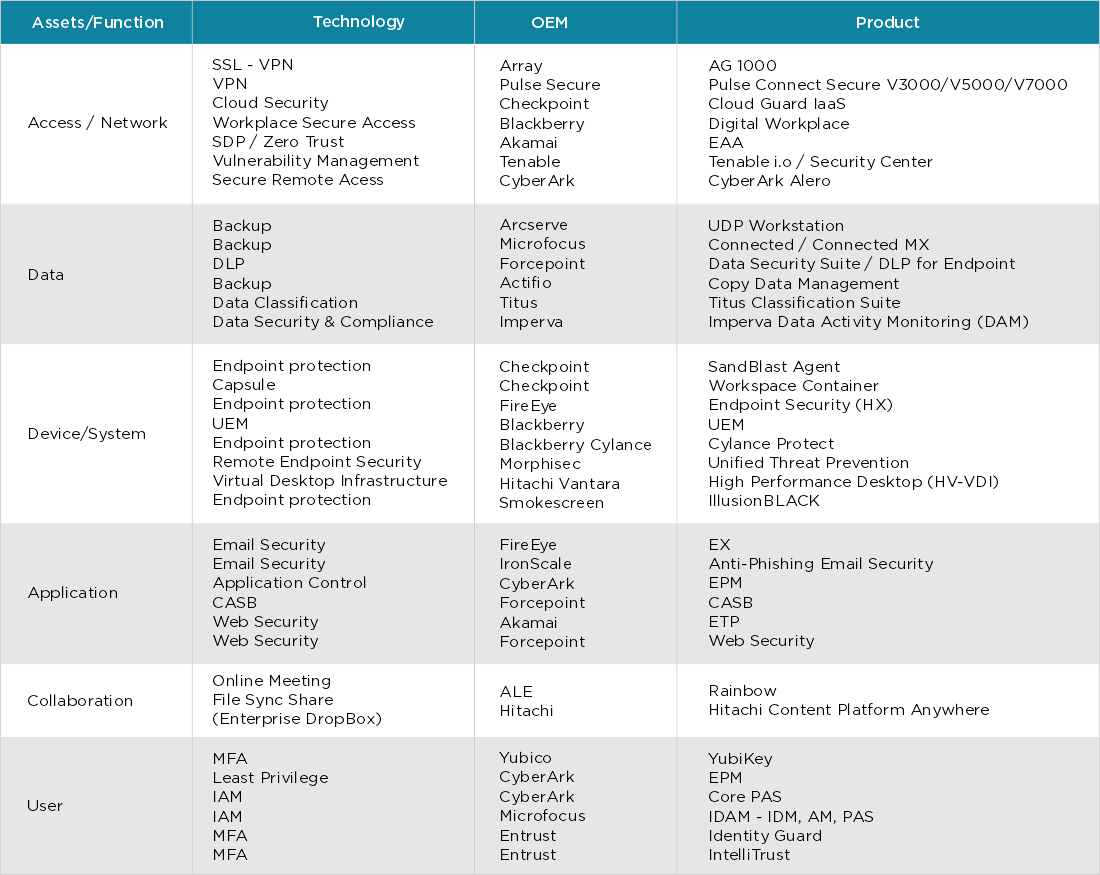
SOLUTIONS
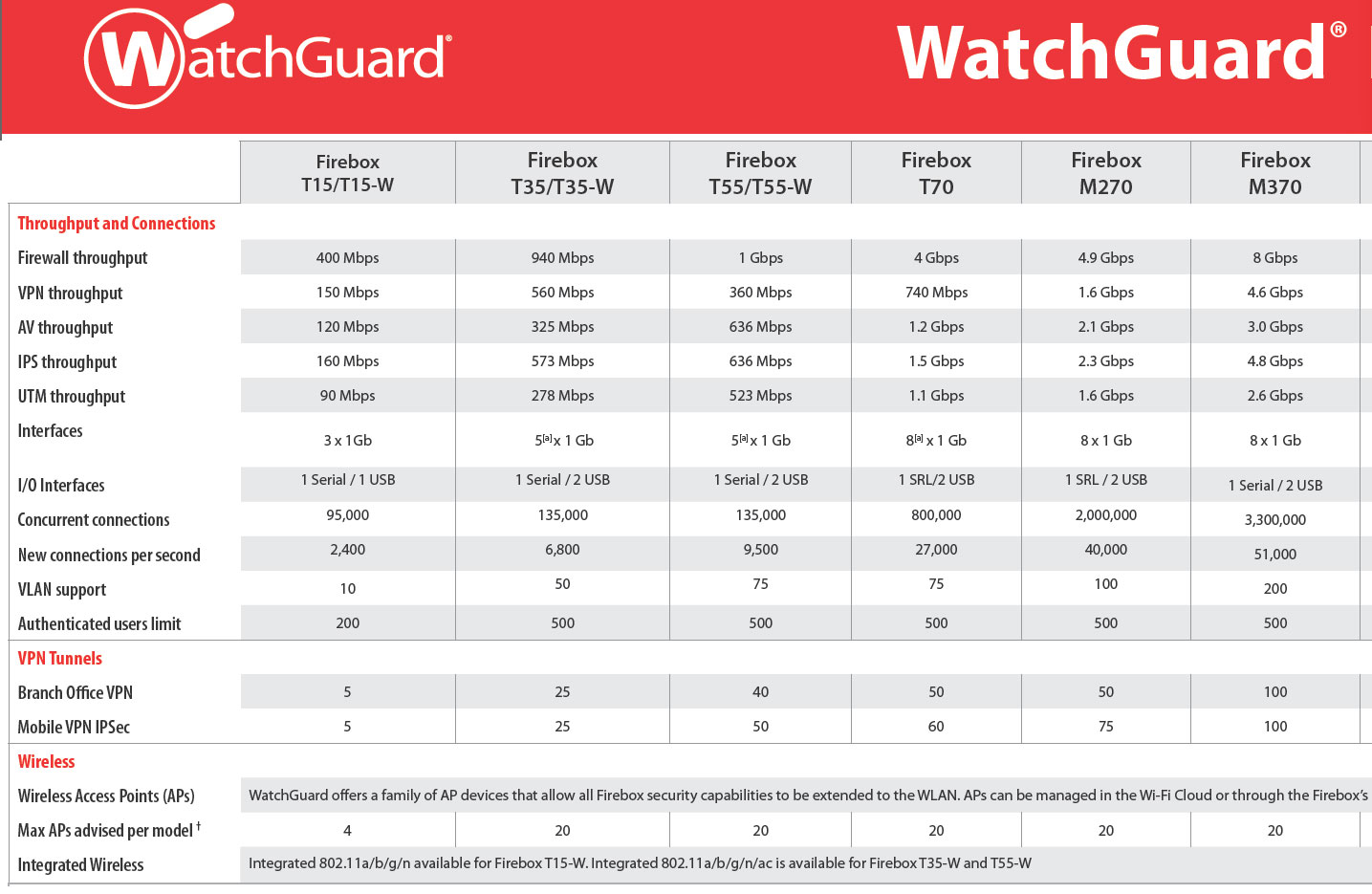
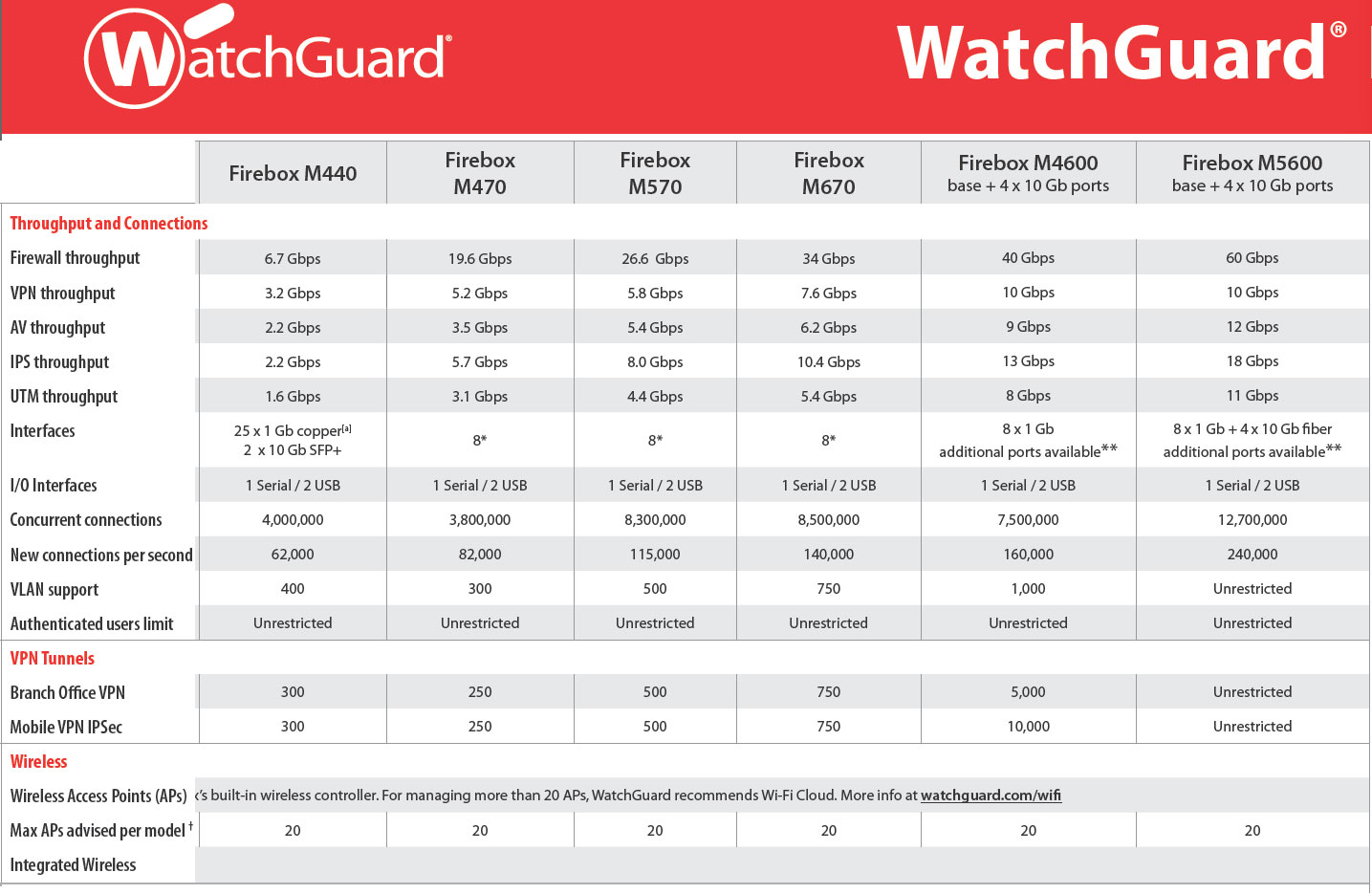
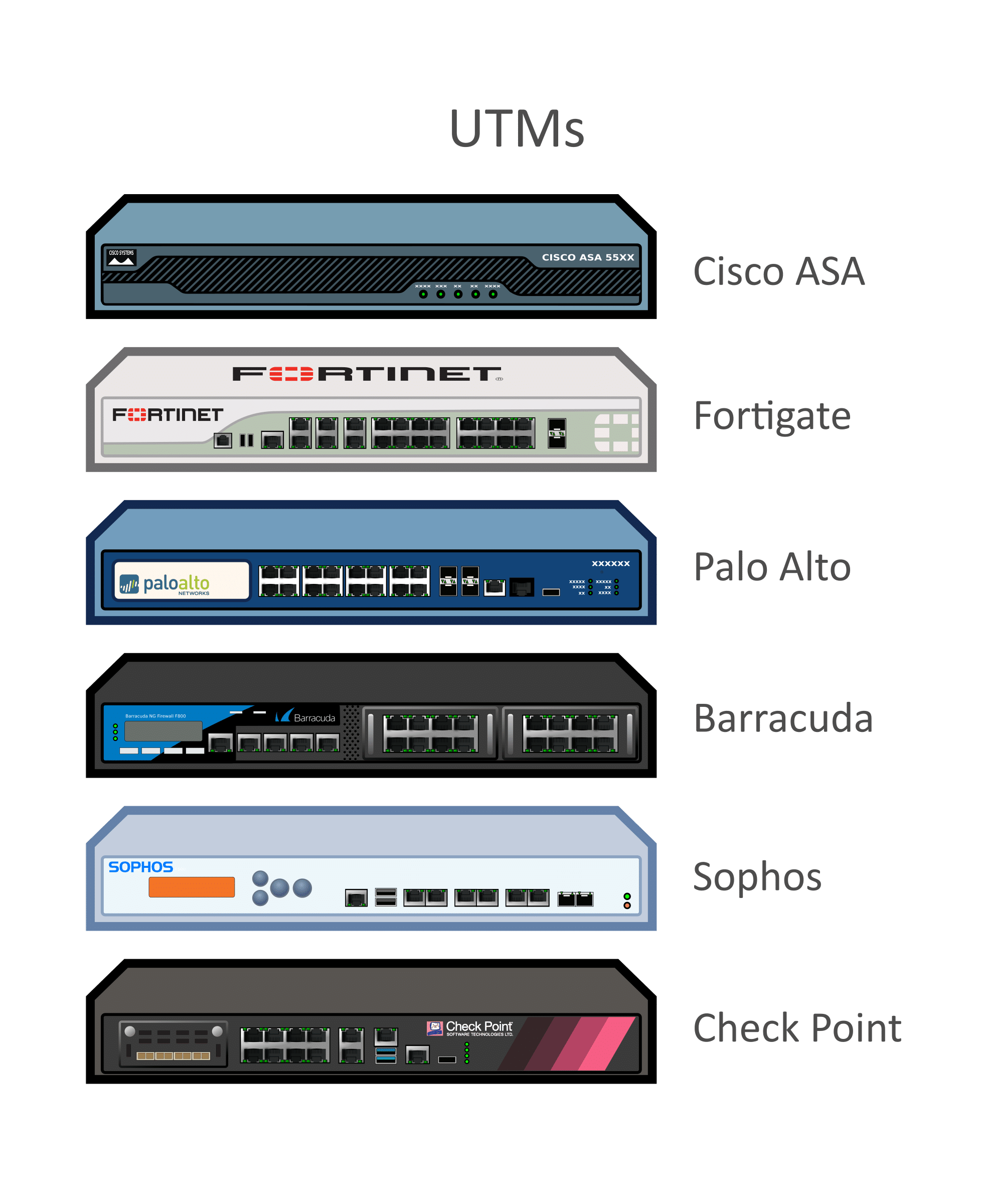
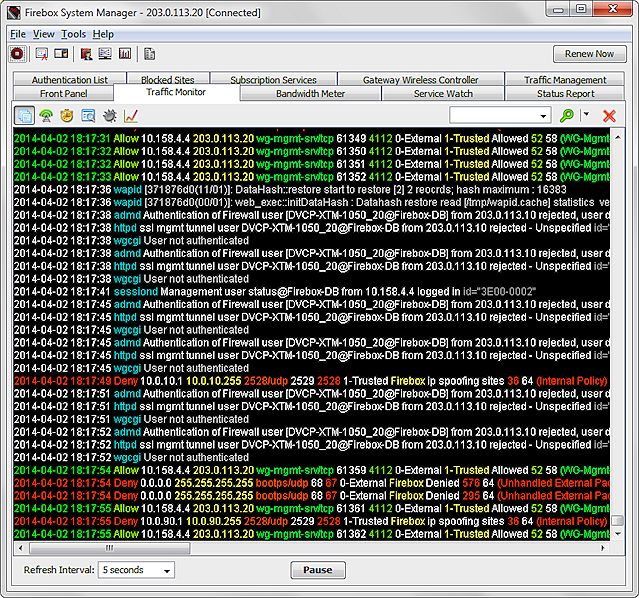
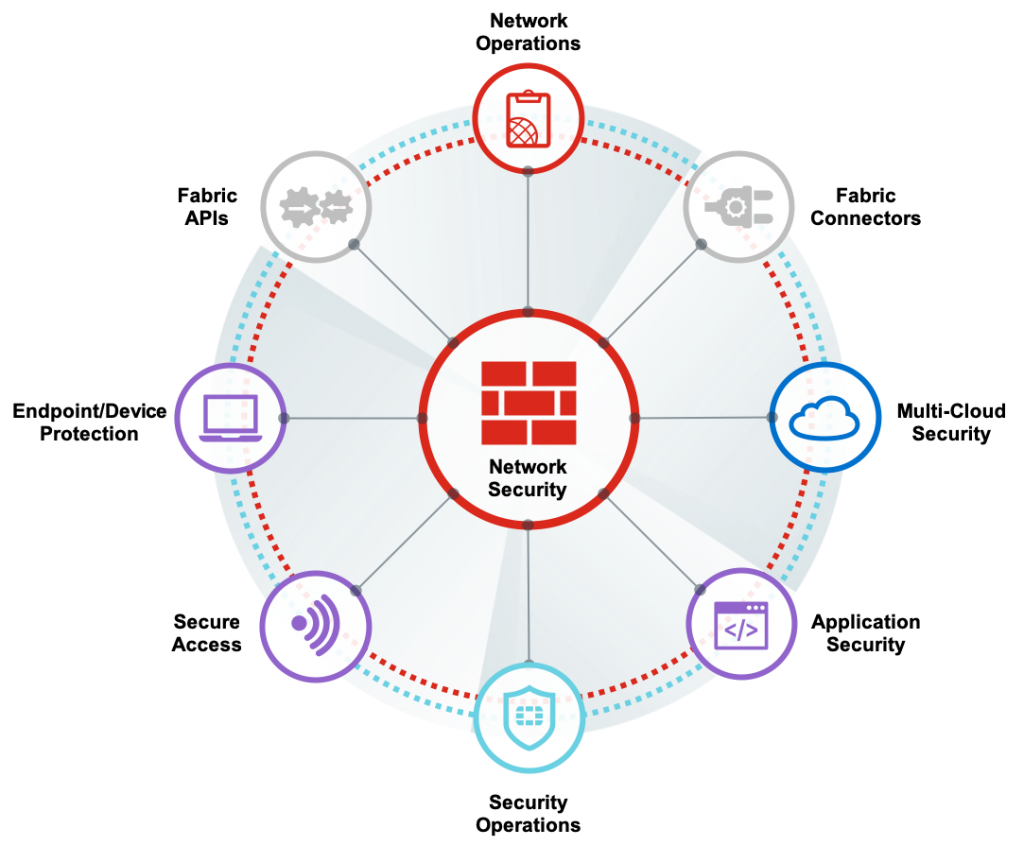
Unified Threat Prevention
Multi-Factor Authentication
Cloud-based Communication
Virtual Secure Access Gateway
Secure Remote Access
Secure VPN
Remote Access VPN
Mobile Security
Endpoint Security
Consultancy Services
Design and Deploy Services
Adoption Services
WORK FROM HOME SOLUTION OFFERINGS
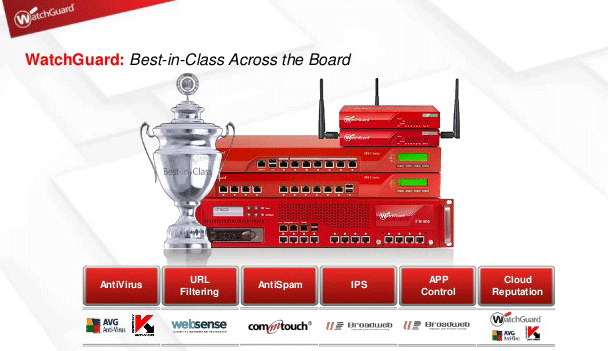
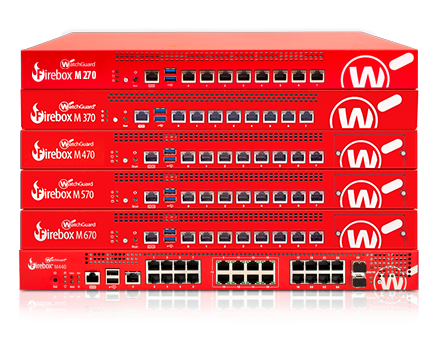
 Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Cyber Security Company in India Provides Next-Generation Firewalls for advanced protection for physical,virtual public,private cloud networks
Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Cyber Security Company in India Provides Next-Generation Firewalls for advanced protection for physical,virtual public,private cloud networks

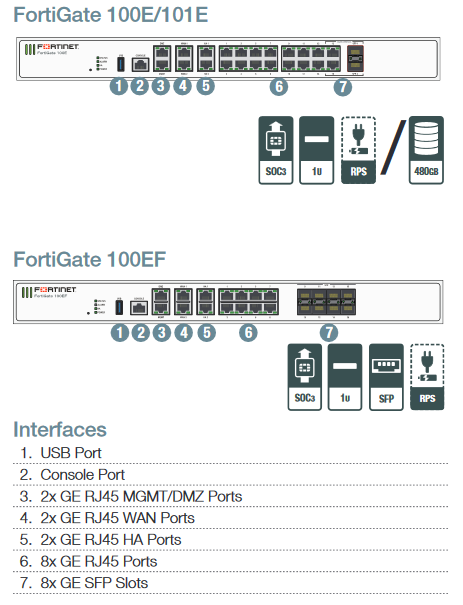
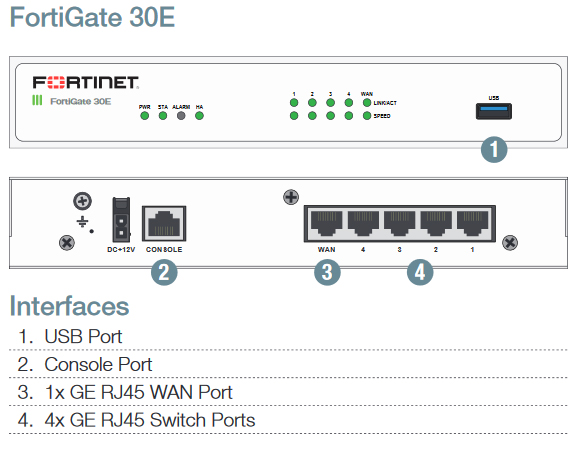 Form Factor – Desktop
Form Factor – Desktop