Persistent malicious attacks exposing cloud infrastructure are the result of a perfect storm combining cryptomining, ransomware and botnet/worms for both Linux and Windows, the Securonix Threat Research Team reported.
“The attack activity described in the report is likely prevalent and mass-scale,” Oleg Kolesnikov told SC Media.
The research Addison, Texas-based Securonix provides further insight into the inner-workings of particularly persistent, not to mention complex, threats to cloud infrastructures.
“Based on what we’ve been seeing in the wild, it has been taking on the order of minutes for new exposed IPs to be compromised by different threat actors using the attack vectors discussed in the report,” said Kolesnikov, who co-authored the report with Harshvardhan Parashar.
Some Xbash botnet attacks, which emerged a few months ago but has been active since May 2018, target multi-vectors and multi-platforms,while others are “fairly trivial,” involving single-vector/single-platform attacks where the focus is mainly on cryptomining,
Xbash malware infects Linux and Windows systems with the aim of deleting critical databases instead of encrypting them without any functionality to backup/recover the files, while installing cryptojacking scripts and impersonating a ransomware attack.
“We are seeing more and more cases where attackers are leveraging multiple different attack modalities as part of the actions on objectives in the same attack campaign,” Kolesnikov explained, adding that the trend is “becoming part of the norm.” Subsequently, blue teams need to be able to deal with such an attack combination on a daily basis, he added.
From a detection perspective, some attacks have been associated with observed Moanacroner and Xbash behaviors. “But these are not the only attacks that were observed exhibiting the behaviors,” Kolesnikov noted.
“In most cases, the focus of the attacks is on installing a second-stage payload for cryptomining and/or remote access,” the report stated. “In other cases, the malware propagates and infects the exposed services,removes data, and installs second-stage cryptomining and ransomware payloads.”
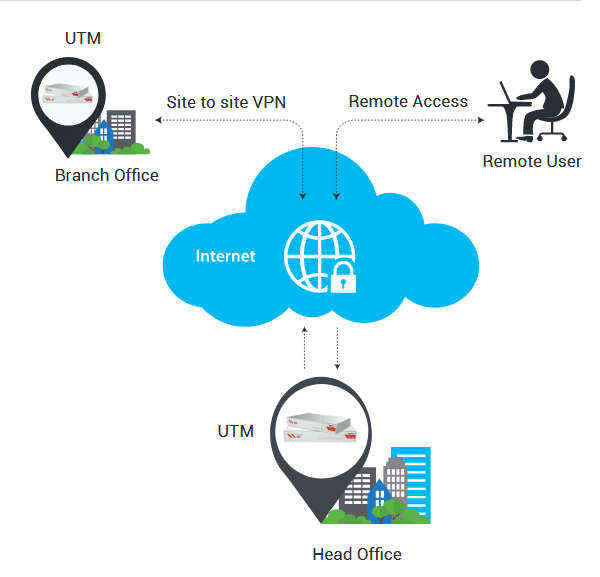
 Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Cyber Security Company in India Provides Next-Generation Firewalls for advanced protection for physical,virtual public,private cloud networks
Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Managed Cyber Security Company in India Firewall Firm is a Cyber Security Company in India Provides Next-Generation Firewalls for advanced protection for physical,virtual public,private cloud networks